Hi,
If you don't know how work the chain of trust for the httpS
You might want to watch this video
https://invidious.privacydev.net/watch?v=qXLD2UHq2vk
( if you know a better one I'm all ears )
So in my point of view this system have some huge concerns !
- You need to relies to a preinstalled store certificate in your system or browser...
Yeah but do you know those peoples ??!! it might seem weird, but actually you should TRUST people that YOU TRUST/KNOW !!
Here an extract from the certificate store om Firefox on Windows.
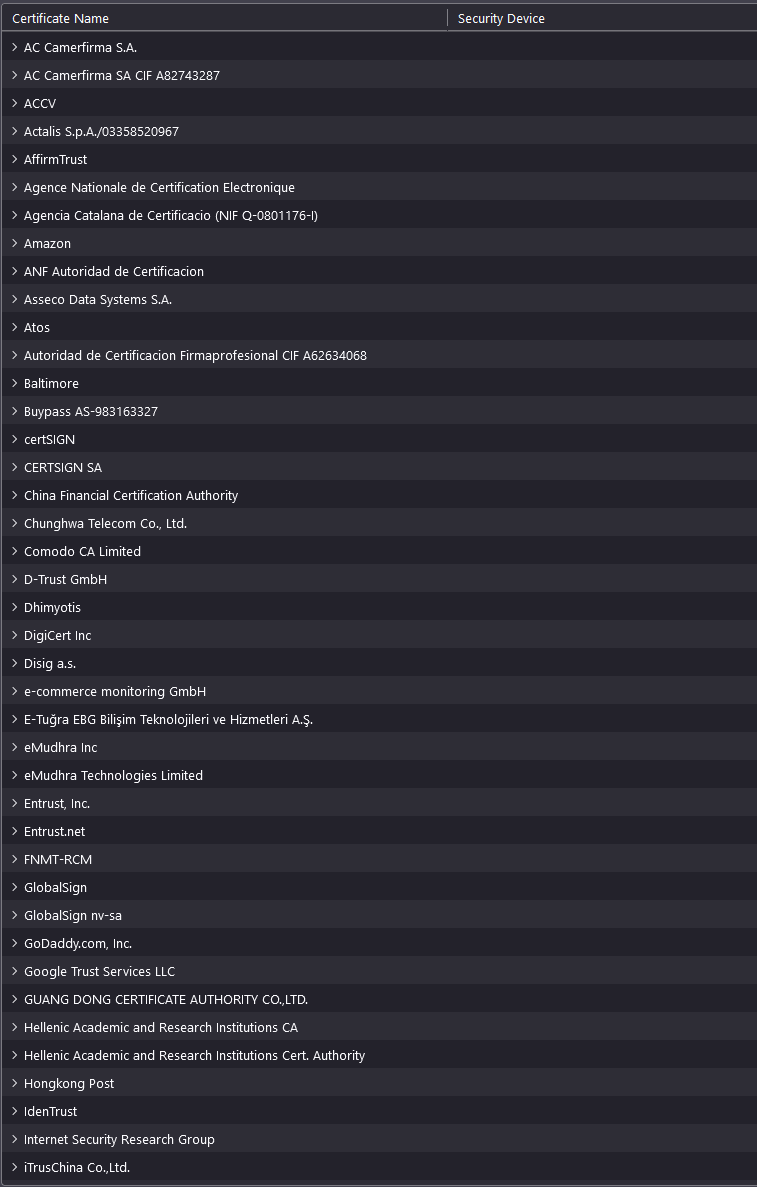
I do not know ( personally ) any of those COMMERCIAL company !
- Of course we could use Self-certificate but this is not protecting against Man-in-the-middle_attack . Instead of using a chain (so few 3th party involved , so increasing the attack surface ! ) why not using something simpler !? like for example
- a DNS record that hold the HASH of the public key of the certificate of the website !
- a decentralized or federated system where the browser could check those hash ?
Really I don't understand why we are still using a chain of trust that is
- not trusted
- increase the surface of attack
- super complex compare to my proposals ?
Cheers,
Why I don't use the term SSL
Because actually httpS now use TLS not anymore ssl
https://en.wikipedia.org/wiki/Transport_Layer_Security
I don't really see how that would help - but maybe you can elaborate how a blockchain solution would help?
Domains depend on cryptographic keys instead of a group of trusted companies. There are blockchain solutions that exist already. [Ethereum Name Service, Namecoin, etc] The problem becomes determining if the client has the correct blockchain or has enough proof that the retrieved records from the blockchain are accurate.
They're not really necessary though, as the current system has worked very well.